You’ve got the Slack workspace. Google Drive, OneDrive, and Dropbox. Email, Google Calendar, and Zoom. That’s everything, right? One more thing: cybersecurity! You need something to encrypt all that information you’re sending and storing on your work computer.
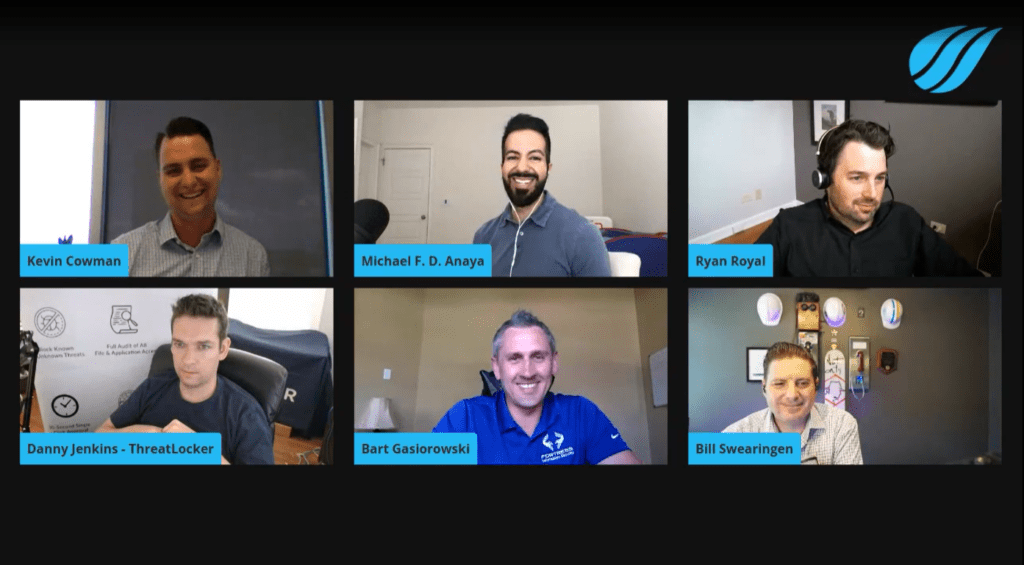
Between January and April 2020, McAfee found that cloud-based attacks rose by a whopping 630%. Kevin chatted with a panel of cybersecurity experts to share how we can keep our information safe while working remotely.
Cyberthreats can be driven by financial necessity
Panelist Michael Anaya, Head of Cyber Risk at Expanse, was a special agent with the FBI for 14 years. He knows a thing or two about security and he says that criminal threat is driven by financial necessity. When major organizations need to save money, one of the first things they might cut back on is cybersecurity. This leaves an open opportunity for cyberattacks.
“If you think about that equation, you have an increase of threats, decrease in security. You’re going to have more breaches. And I think that’s one of the things that companies and organizations at large need to be mindful of,” Michael said. “If you’re going to cut back on IT or cybersecurity funding, how are you going to make up for the increase in terms of your threat vector?”
Bill Swearingen, Security Strategist at IronNet Cybersecurity, mentions that organizations need to make sure they’re protecting company assets early on. Employees might be connected to less secure networks when they’re working remotely. They might also be downloading files in new locations rather than in the office’s central location.
“The threat landscape has changed,” Bill said. “You’ve gone from known locations where your employees will be accessing to hundreds or thousands of different locations. Each one of those networks should be treated as a hostile network. You have that criminal threat rising. You have a decentralized workforce that might be an easier target.”
Be proactive with client onboarding and adjusting processes
Ryan Royal, CTO at Interviewstream, shared how client solutions shifted to an online-only format and how the company responded to this change.
“As soon as the pandemic hit, everybody made sure they shifted all of their recruiting needs, hiring needs, and interviewing needs online,” Ryan said. “That was our main focus: How do we 1) provide the service level that they’re expecting, and 2) make sure it was secure.”
Be proactive with your communications so you’re staying on top of showing clients how to do things and easing them into the transition. Ryan and his team ran disaster recovery exercises to test what worked with their system and tweaked what needed improvements.
Onboard your clients remotely with a structured process. Make sure clients can use your platform in a way that’s as easy as possible with the least amount of resistance.
Run through a compliance checklist
Danny Jenkins, CEO and CoFounder at ThreatLocker, had to handle extra demand after the national shutdowns. His company received more cybersecurity requests than ever. To combat this, he ran phishing tests with third-party vendors.
“We go through all these compliance checks, and one of those checkboxes is, ‘Have you had plans and contingencies for a pandemic or outbreak?’” Danny said. “And when we go through that, it’s almost like when you watch the video on the plane saying, ‘This is how you put your mask on.’ It’s not even something that’s comprehended. When you see that checkbox, it’s not real, it’s just a compliance checkbox.”
That compliance checkbox turned into a real test this year as the need for cybersecurity skyrocketed.
Provide your team with the best equipment
Bart Gasiorowski, VP of Fortress Information Security, says this level of security and running additional tests was new for a lot of people. Companies take these precautions in the office, but moving from in-office to remote environments took some adjusting to make sure everyone was on the same page.
“I don’t think anybody anticipated what we’re going through right now,” Bart said. “Going through our policies and making sure they’re up to date…And it’s a communication thing company-wide, giving the awareness to your employees on using the VPNs and not using personal laptops.”
Bill also mentioned that keeping your work computer separate from your personal computer can help separate work from play, and your work can be more secure with your company’s cybersecurity plan.
“There’s a delineation between where the work is done,” Bill said. “This workspace is also part of the home, so it changes that dynamic of that separation and that disconnection between home and work.”
Danny says the hiring process for ThreatLocker is much different now. Instead of coming into the office, meeting the team, and filling out paperwork, the company sends a link for the paperwork and a link to join the team on Zoom calls (side note: that’s what I did when I joined BlueWave!).
“Your responsibility as a business owner is to make sure you hire the right people, from an IT perspective and from an inside perspective as well,” Danny said.
He recommends leveraging resources to get the equipment you need for your employees. When computer brands sell out, tap into your company partnerships, and see what equipment is available.
Keep an eye on burnout
Working from home might lead to more time staring at screens and forgetting to take breaks. Employees are more inclined to work longer and take less PTO days when they’re at home. This is where managers come in, reminding people to take time for themselves.
“One of the things we’re trying to tackle is trying to get ahead of the curve when people start burning out,” Michael said. “Giving people back their personal time, telling them to take some time for yourself. Just relax. Listen to a podcast or watch 6 guys talking about cybersecurity.” 😏
For many employees, gone are the days of long commutes with music and audiobooks. Now, the start of the workday is just a few steps away.
“When you commute, you have downtime,” Michael said. “You can sit in your car, listen to the radio, call a friend. All those things that in the current state of affairs, it doesn’t happen. I get there in record time, but there’s no downtime.”
Taking time off can also help team members rest their minds to return feeling refreshed.
“Make sure your focus is still on the threat. Make sure you’re in that right mindset and can give your full attention to your job,” Bart said.
How to keep your team safe
This might seem obvious, but don’t click on suspicious links. Avoid responding to emails that look like they could be spoofing someone’s real email address. Don’t give attackers that opportunity.
One of the most common scams in hiring can be resume emails loaded with malware. If someone asks you to download a file or take action outside of a secure platform, that’s a big sign to mark the email as spam and delete it. Be proactive, and don’t make your team vulnerable.
“We’ve coined the name ‘Fake Charlie’ who preys on our newer employees and asks them to run an errand or buy a gift card,” Kevin said.
Every company has encountered a Fake Charlie at some point. According to Bryan Krebs, the number one rule in online safety: “If you didn’t go looking for it, don’t install it!”
“We have to ensure we have strong visibility and strong defenses to be able to detect these attacks,“ Bill said.
Your team can also check out the Small Business Association website for specific guidelines in keeping your team safe and preventing cyberattacks.
“Use the checklist. Question your IT team and how they’re dealing with backup, preventing phishing attacks, to monitor and secure your systems,” Danny said.
Need to build your team in a safe, remote environment?
We’ve got you covered! We’re here to learn what positions you need to fill and get to know your company culture. Contact our team today to find top-notch talent for your company.



